Monday, June 1, 2020
My thanks to Vision Smarts for sponsoring the blog this week.
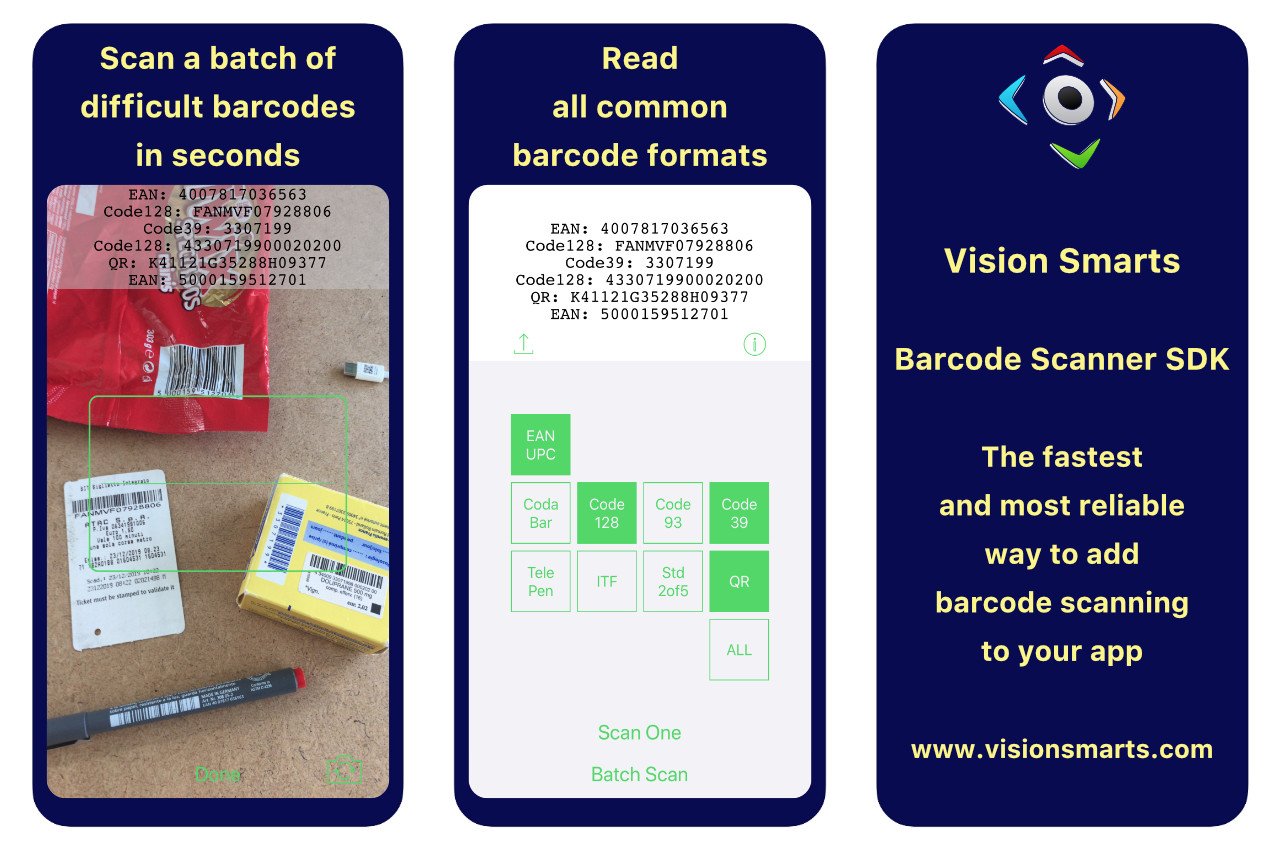
The Vision Smarts Barcode Scanner SDK for iOS and Android has been powering high-volume apps in retail, banking, logistics, nutrition, and more, for ten years.
Its proprietary algorithms have been continuously optimized for smartphone and tablet apps that need to read barcodes from all origins and of all sizes, even when they are dirty, faded, bent, damaged, or printed at low resolution.
Vision Smarts, an engineer-led company, strives for maximum simplicity and efficiency at every level. The binary library is lightweight with no dependencies, no tracking, no network access. The API is just one method, and the SDK includes the source code of the demo app to get you up and running fast. Licensing and pricing are straightforward: a flat annual fee per app, no gotchas.
A showcase app is available on the App Store and Google Play. Please try it on the hardest barcodes you can find and let its developers know what you think!
Android iOS iOS 13 Programming Sponsor
Juli Clover (also: Mr. Macintosh, Hacker News):
According to the security notes for the update, it addresses a security flaw that could allow an application to execute arbitrary code with kernel privileges.
This is the same vulnerability that has been addressed in today’s iOS 13.5.1, tvOS 13.4.6, and watchOS 6.2.6 updates, and it allowed for the unc0ver jailbreak that allegedly works on all versions of iOS, including iOS 13.5.
It’s also patched for macOS 10.13 but not for 10.14, which supports the theory that this was an old bug that got fixed in iOS 12 and macOS 10.14 and then came back.
Luca Moro (via Jeff Johnson):
During late 2018, we published the details about a XNU kernel vulnerability that we dubbed lightspeed.
This vulnerability started as a racy UaF in the syscall lio_listio that allows the liberation of a kernel object twice.
You can read all the details about it in our post.
This vulnerability was patched early in iOS 12 and 11.4.1 was the last vulnerable iOS version.
[…]
In the blogpost we explained that, while the issue was fixed, a memory leak was introduced, and it was now possible to force the kernel to panic.
The APFS bug from macOS 10.15.5 does not seem to be fixed, but Carbon Copy Cloner has found a workaround.
Previously:
Bug Carbon Copy Cloner Exploit iOS iOS 11 iOS 13 Kernel Mac macOS 10.13 High Sierra macOS 10.15 Catalina
Philipp Defner (also: Hacker News):
Since macOS 10.12 there’s a bug in Apple Mail that causes it to randomly become the frontmost application. If you are in full screen mode — like when you are giving a talk or watching a movie — it opens itself up in split view mode where it takes up half the screen while your other main window is being resized.
[…]
After some research it became clear that it’s related to Gmail and I’m not exactly the only one[…]
As a developer of a Mail plug-in, I’ve been hearing about this for years. People assume it must be caused by third-party software, but in fact it can occur with a clean macOS installation. I’m not sure that it’s limited to Gmail accounts. It may just affect more Gmail users because (a) there are a lot of Gmail users, and (b) Gmail’s IMAP implementation is particularly unreliable, often unavailable for short periods of time.
vladharbuz:
It seems to happen because of improper error handling. If you look closely at the app in the instant it opens, your affected account will have a “disconnected” symbol next to it in the sidebar. However, it goes away before an error can be shown.
My theory is: there is a momentary connection issue with these G Suite accounts, and Mail.app starts to show an error by focusing itself, but the error is resolved so quickly it doesn’t actually get to show the “connection problems” modal.
evanelias:
In my experience, if you always hide the Mail window (cmd-h) instead of closing it (cmd-w), it won’t ever pop back up. Takes a while to retrain the muscle memory though!
Update (2020-06-02): mkalina:
Not only with Gmail. Same happens with O365/Exchange, too.
Apple Mail Bug Gmail Mac macOS 10.12 Sierra macOS 10.13 High Sierra macOS 10.14 Mojave macOS 10.15 Catalina
Peter Steinberger (tweet):
InterposeKit is a modern library to swizzle elegantly in Swift. It is well-documented, tested, written in “pure” Swift 5.2 and works on @objc dynamic Swift functions or Objective-C instance methods. The Inspiration for InterposeKit was a race condition in Mac Catalyst, which required tricky swizzling to fix, I also wrote up implementation thoughts on my blog.
Instead of adding new methods and exchanging implementations based on method_exchangeImplementations, this library replaces the implementation directly using class_replaceMethod. This avoids some of the usual problems with swizzling.
You can call the original implementation and add code before, instead or after a method call.
Peter Steinberger:
imp_implementationWithBlock has no way to undo or deregister the IMP; so once you submitted a block that captures state, you have a permanent memory leak? Oh well.
Catalyst (Marzipan) iOS iOS 13 Mac macOS 10.15 Catalina Memory Management Objective-C Objective-C Runtime Open Source Programming Swift Programming Language
Bhavuk Jain (via MacRumors, Hacker News):
In the month of April, I found a zero-day in Sign in with Apple that affected third-party applications which were using it and didn’t implement their own additional security measures. This bug could have resulted in a full account takeover of user accounts on that third party application irrespective of a victim having a valid Apple ID or not.
For this vulnerability, I was paid $100,000 by Apple under their Apple Security Bounty program.
[…]
I found I could request JWTs for any Email ID from Apple and when the signature of these tokens was verified using Apple’s public key, they showed as valid. This means an attacker could forge a JWT by linking any Email ID to it and gaining access to the victim’s account.
See also:
Previously:
Bug iOS iOS 13 open Privacy Security Sign In with Apple
Paul Rosania:
Amazon order confirmations and shipment notifications no longer include any item details. I could not for the life of me figure out why they would do this. They’re not scored on MAUs, they don’t need me to click through. Then I realized: is it so Google can’t see my order data?
I’ve been wondering about this for a while. It’s really annoying not to be able to search one’s own order history. I end up printing each order confirmation Web page to PDF.
Andrew Chen:
my guess- it’s not for google, but bc there’s email analytics cos that estimate sales of individual products based on parsing emails
At Uber, we used parsed competitor receipt data to estimate for instance, airport mkt share %, short trips mkt share etc
Previously:
Update (2020-06-02): John Gruber:
One reason this change was merely a low-grade annoyance for me, personally, is that I allow the Amazon iPhone app to send me notifications, and these notifications include shipping updates and delivery confirmation. […] And Amazon’s website and app continue to have a nicely searchable archive of your entire order history — mine goes back to the Clinton administration, which feels like another epoch. But it was nice having your own searchable archive of purchased items right in your email.
Stephen Swift:
You can also export your Amazon order history as CSV.
Update (2020-06-09): Matt Henderson:
This is annoying for me, because I always create an OmniFocus “Waiting for…” task attached to the Amazon confirmation emails. Now that the emails don’t include the order details, I can’t do that any longer. So annoying.
Amazon E-mail Shopping Strategy Tax Top Posts Web